
Privacy, Law & Policy Affiliate | Protecting Yourself from Digital Stalking
Have you ever felt like someone knew where you were without communicating it to them, or that information is being used against you? Then join us for this discussion! We […]

Have you ever felt like someone knew where you were without communicating it to them, or that information is being used against you? Then join us for this discussion! We […]

Join one of our information sessions to learn about participating in the next phase of the State of Inclusion of Women in Cybersecurity. Each session will provide an overview of […]
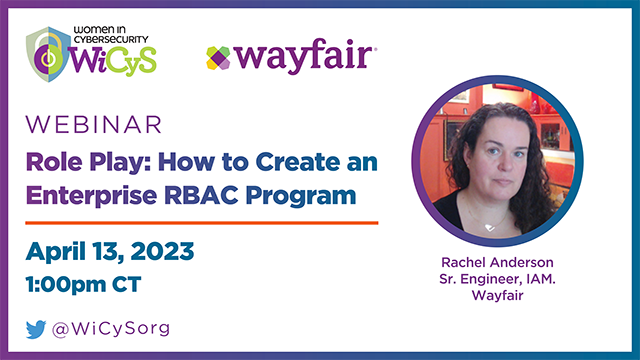
When a new hire joins, they should get immediate access to the tools needed to perform their job. Similarly, when they change jobs their access should adapt and change. This […]

In this chalk talk, learn why continuous compliance is important and how WiCyS strategic partner AWS validates our compliance internally with Annie Chatterji. We discuss the basics of continuous compliance, […]

Join one of our information sessions to learn about participating in the next phase of the State of Inclusion of Women in Cybersecurity. Each session will provide an overview of […]
This group meets monthly, the last Wednesday of each month to talk about mindfulness and career development strategies in a supportive group setting. Hosted by Nathali Cano. Register HERE.
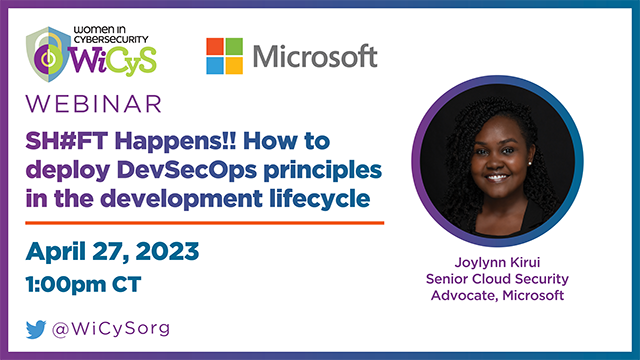
With every commitment, the threat landscape increases. One single vulnerability is all a hacker needs. Vulnerabilities have multiple sources, and you must have a plan for securing each potential risk […]

Join us in this WiCyS strategic partner webinar with LinkedIn for an exciting journey through the evolution of LinkedIn's bug bounty program. Discover the ins and outs of bug bounty […]

Here's your opportunity to network with like-minded individuals who work in the field of, or are interested in cybersecurity. Meet our team! Get to know the board members of WiCyS […]
WiCyS Phoenix will be hosting a virtual event to shed light on the five laws of cybersecurity. Nick Espinosa is an expert in cybersecurity and network infrastructure, he has consulted […]

Join WiCyS's strategic partner Lara Goldstein from Microsoft to learn best practices for securing CI/CD pipelines to prevent software supply-chain attacks. Register HERE.

Join us for an informational webinar for the WICYS + ISC2 Certified in Cybersecurity Certification Summer Camp. The WICYS + ISC2 Certified in Cybersecurity Certification Summer Camp will take 500 […]