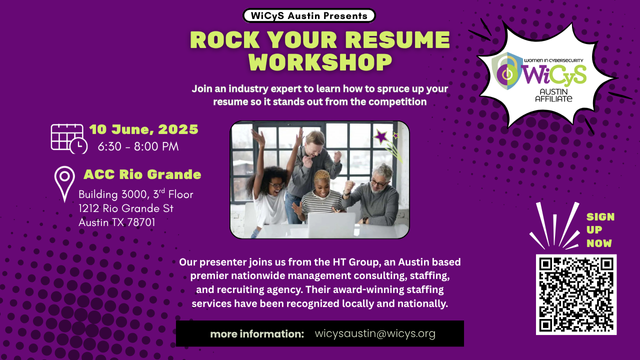
WiCyS Austin Affiliate | Rock Your Resume Workshop
Join the WiCyS Austin Affiliate at Austin Community College: Rio Grande Campus for an exciting event to amp up your resume game! Whether you're a seasoned professional or just starting […]
Join the WiCyS Austin Affiliate at Austin Community College: Rio Grande Campus for an exciting event to amp up your resume game! Whether you're a seasoned professional or just starting […]

The Google Cybersecurity Professional Certificate Cohort Program is a nine-course series that was developed to provide an understanding of the importance of cybersecurity practices and their impact on organizations. Learners […]

Join our Wisconsin Affiliate at the 2nd Annual Milwaukee Cybersecurity Summit to connect with WiCyS members. Please stop by our booth to meet our affiliate, snag some swag, and learn […]

WiCyS Ontario and TruNorth are excited to co-host Byte Sized Connections, a relaxed, in-person networking evening for cybersecurity professionals. This is a great opportunity to meet others in the field, […]

Join our Phoenix Affiliate at INTERFACE Phoenix to connect with WiCyS members. Please stop by our booth to meet our affiliate, snag some swag, and learn more! IT Infrastructure is […]
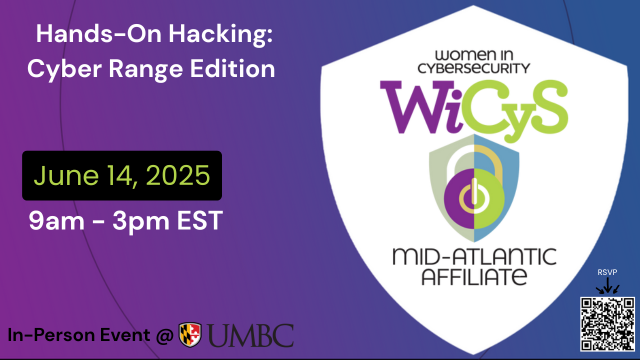
Please join us for fun, networking, socializing, guest speakers, and hands-on practice at the Cyber Range, an event organized by UMBC and WiCyS MidAtlantic. Don't forget to bring your own […]
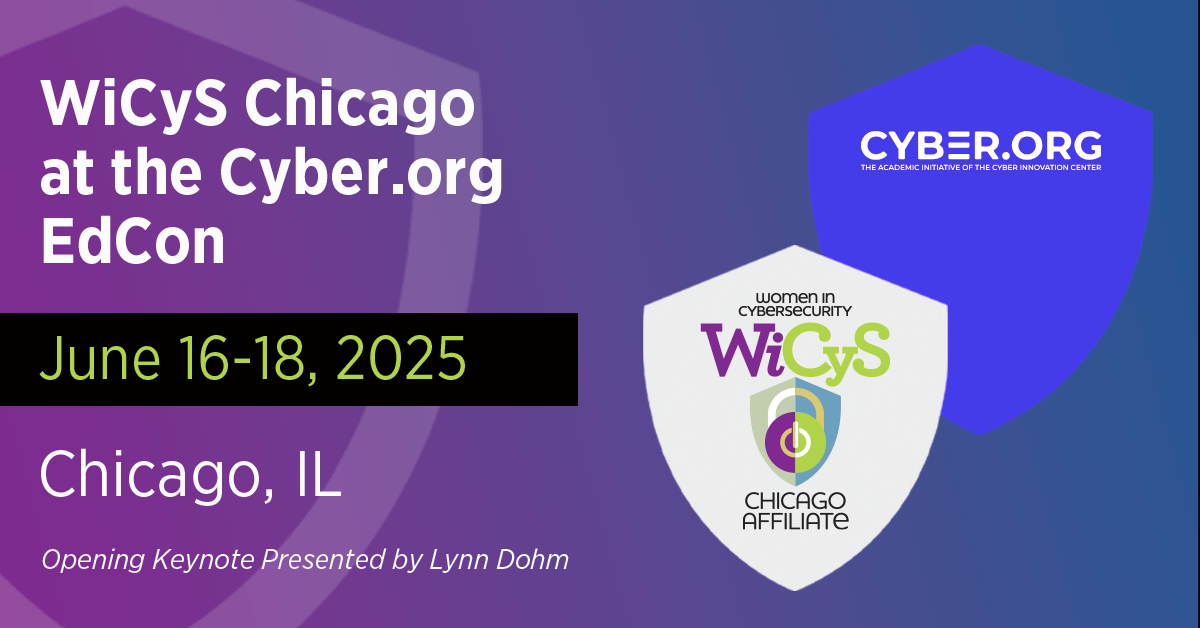
Join WiCyS Executive Director Lynn Dohm as she delivers the opening keynote "The Educator's Edge: Igniting the Spark of Cybersecurity for the Next Generation" for Cyber.org EdCon 25. Please stop […]

Join WiCyS Strategic Partner SentinelOne at re: Energize with SentinelOne at re: Inforce 2025 during the AWS re: Inforce conference, June 16- 18th. Don't miss this networking opportunity to meet […]

Not all security careers are deeply technical—some are built on effective communication, empathy, and the ability to form strong, lasting partnerships. In this session, Catalina Michaela Toea, Manager of EMEA […]

Explore how to evaluate and manage the security risks of integrating third-party AI/ML tools. This session will focus on supply chain considerations, vendor risk assessments, and strategies for maintaining trust […]