
WiCyS Strategic Partner MeetUp
WiCyS Strategic Partner MeetUp: Strategic partners are the foundation of all WiCyS programs, initiatives, and events. Not only are they committed to the growth of the organization, but they also […]

WiCyS Strategic Partner MeetUp: Strategic partners are the foundation of all WiCyS programs, initiatives, and events. Not only are they committed to the growth of the organization, but they also […]
Leading with equity, inclusion, and allyship is a conversation where we, as volunteer leaders within the WiCyS organization, agree to engage in a conversation from a place of consent for […]

WiCyS Student Chapter Leaders-Only Meeting: WiCyS Student Chapters are developed and launched at a rapid rate around the world and help showcase the collective strength of the Women in the […]

WiCyS Professional Affiliate Leaders-Only Meeting: We are all Stronger Together. As WiCyS professional affiliates trailblaze through their regional, specialty, or corporate affiliate programs, we collectively meet monthly in a leadership […]

WiCyS Professional Affiliate Leaders-Only Meeting: We are all Stronger Together. As WiCyS professional affiliates trailblaze through their regional, specialty, or corporate affiliate programs, we collectively meet monthly in a leadership […]

WiCyS Professional Affiliate Leaders-Only Meeting: We are all Stronger Together. As WiCyS professional affiliates trailblaze through their regional, specialty, or corporate affiliate programs, we collectively meet monthly in a leadership […]

WiCyS Cybersecurity Steering Committee Meeting: Cybersecurity matters in the nonprofit space. Led by the WiCyS vCISO, this committee meets bi-monthly to drive the effort of the cybersecurity efforts and standards […]
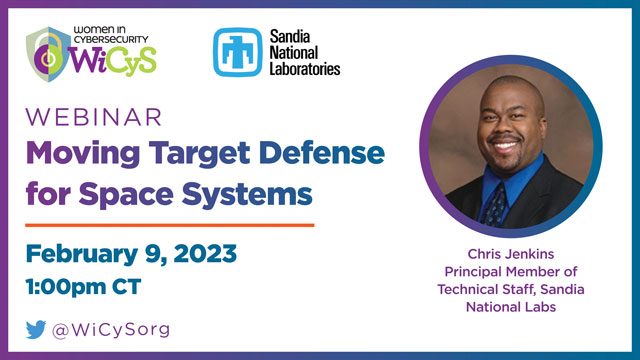
Space systems provide many critical functions to the military, federal agencies, and infrastructure networks. Space Policy Directive-5 Cybersecurity Principles for Space Systems describes the cyber threat to space systems and […]

IT and security leaders need to find a method to stay ahead of adversaries as ransomware gangs continue to hone and ramp up their operations. As successful assaults increase, it […]

Optum, the technology, and services division of UnitedHealth Group and WiCyS strategic partner, is back to take over the WiCyS Instagram Story! This time, we'll be joined by Kathleen Boyle, […]
Join the WiCyS Neurodiversity Affiliate and Founder Tennisha Martin, Executive Director and Chairwoman of Black Girls Hack in a discussion about Black women in cybersecurity, the state of the industry, […]
WiCyS Phoenix has been invited to attend this conference FREE of charge. Connect with [email protected] for the FREE Admission code.