
WiCyS DevSecOps Affiliate | The Cloud Security Intermediate Bootcamp
Are you new to Cloud or Security topics? Are you interested in growing your knowledge of Cloud or Security technologies and concepts? Have you ever worked with the AWS cloud […]

Are you new to Cloud or Security topics? Are you interested in growing your knowledge of Cloud or Security technologies and concepts? Have you ever worked with the AWS cloud […]
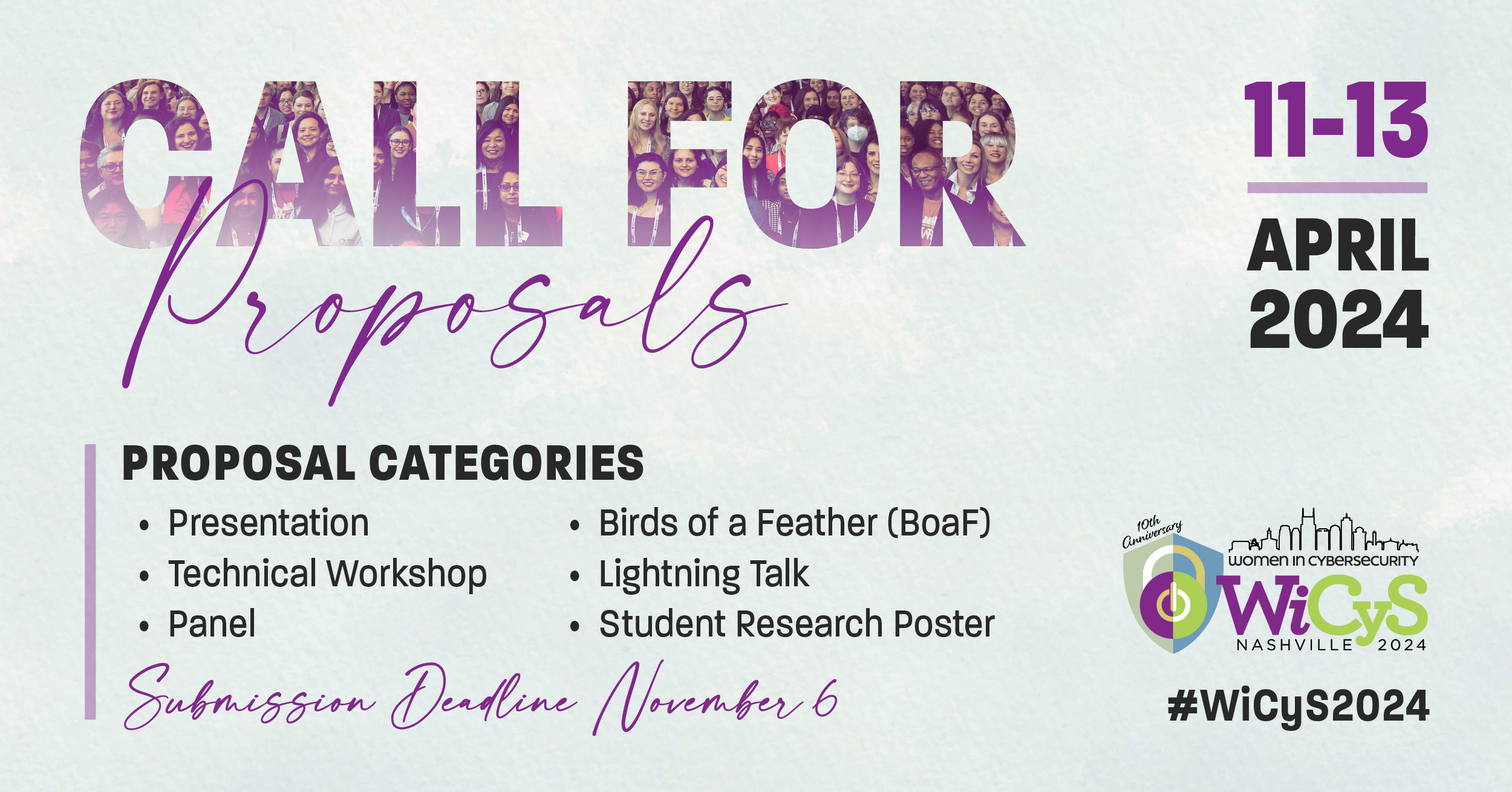
Help showcase the strength of women in cybersecurity by submitting a workshop, lightning talk, presentation, birds of a feather, panel or student research poster for the 10th anniversary of our […]

You're invited to network and grow your skills at the annual Women in CyberSecurity (WiCyS) technical conference April 11-13 in Nashville, TN. Apply for reduced conference rate registration and two nights of […]

This series focuses on how to ensure your personal cybersecurity. Our goal is to help educate and empower our community with resources, tips, and tricks to ensure safe and secure […]

Learn best practices for protecting yourself during our WiCyS Cybersecurity Month webinar series, Real Ethical Hacking Stories. This webinar series will give viewers insight into real-life scenarios, awareness of the […]

We are thrilled to share that WiCyS and RSA have joined forces to offer an incredible opportunity to one of our student members. The recipient of the RSA Conference Security […]

It is exciting to announce our partnership with the esteemed Cyber Security Summit 2023, which will take place on October 19th at Croke Park in Dublin. We invite you to […]

Join WiCyS at the State of Texas which has been leading the way in cutting-edge cybersecurity solutions and hear Lynn Dohm at Public Sector Network: Government Cybersecurity Roadshow Texas. This […]

Learn best practices for protecting yourself online and hear hacking stories from the experts themselves during our WiCyS Cybersecurity Month webinar series, Real Ethical Hacking Stories. This series will give […]

It’s the middle of the night. Your phone rings. Your heart sinks as the person on the other end reads you the ransom note. All your data is encrypted—even your […]